This is my second note about Xiaomi Aqara smart home stuff. Something tells me it’s not the last one. In this note I’ll tell about implementing home automation that will reliably work offline using readily available hardware from Xiaomi and (at the same time) keeping your privacy intact. After all, not everyone is ready to share all the private stuff with some corporate crooks 😉

So, how does this stuff work?
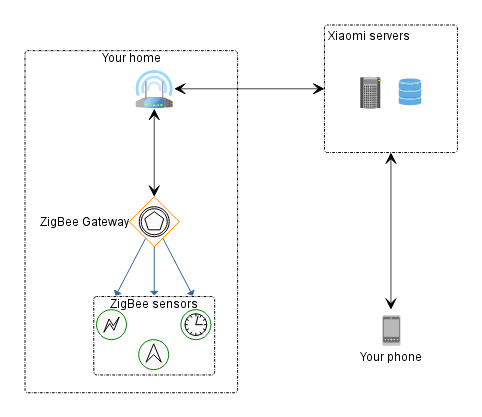
Let’s start by dissecting and documenting the architecture of this whole automation solution. In terms of hardware, it consists of a hub, the round thing you plug into your mains socket and that serves as a gateway between ZigBee network and WiFi. All sensors and other home automation devices are hooked to this ZigBee hub. You should also have a WiFi router somewhere around that will provide you with a stable and reliable internet connection. That pretty much sums up all the hardware that is installed in your home.
So, how does this thing connect with the mobile app, send notifications, etc? Every single operation, including automations is routed via Xiaomi servers. In other words, you press a button on the screen of your cellphone to turn the lights on, the packet-o-data flies to china, from there it flies back to the ZigBee hub, and from there – to the wireless switch that turns the light on. Simple, right?
What’s worse, all automations live there, on the servers. Apart from a terrible lag, leaking a handful of your private data to some corporation, that leads to a very idiotic situation: If you water leak sensor goes off, the automation to turn off the valve will not work if your internet is down. The gateway is dumb and just gets the instructions. Epic fail (and a flood!). Finally, if Xiaomi decides to retire this solution and turn off the servers (Either if they go bankrupt, or decide to clear the market for some “new generation stuff”) – users are screwed: all the hardware immediately turns into pumpkins useless pieces of plastic. Epic fails like that have already happened before.
Automation server (HomeAssistant)
So, either way we’ll get into setting up this one. If we want our automation to work reliably, including the hard times the internet is down, we’ll end up installing and setting up our own home automation server. In reality, HomeAssistant (a.k.a. hass) is not the only available choice around. However it’s (IMHO) the only sane solution. I won’t document the whole setup process here, the official docs are pretty good.
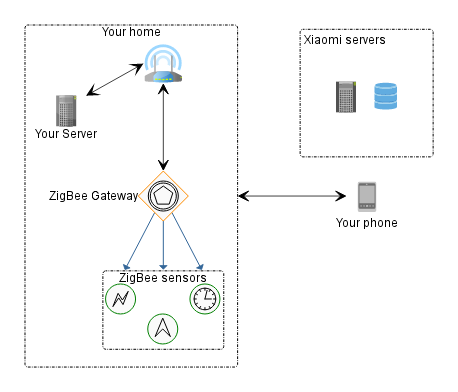
So, our Zigbee hub will communicate with HomeAssistant and NOT the Xiaomi servers, and that’s precisely what we want. By the way, hass supports not only Aqara, but a handful of other devices, including generic mqtt solutions and homebrew esp8266/esp32 stuff. Therefore it’s really worth checking it out. In terms of resources it’s not really hungry, so Raspberry Pi (Got a ready to use firmware), or a stronger Odroid-X2 (that’s my case!) or even an old android tv-stick repurposed as a linux server would do fine. For Odroid-X2 I ended up getting power consumption at about 2-3 watts.
Option 1: Let’s use original Aqara Zigbee gateway
If we use Xiaomi Aqara, getting the hub to work with Home Assistant is not an easy job and requires some voodoo magic procedures. HomeAssistant wiki links us to domoticz documentation (Another home automation server) that describes all the required steps.
In short, we have to:
- Turn on developer mode in the Xiaomi mobile app (Yep, we won’t get around registering there, setting our location to ‘China Mainland’ and adding the ZigBee Hub)
- After that magic, the hub exposes a REST API to the local network. HomeAssistant will use it.
- We write down the API key to our configuration.yaml of HomeAssistant
- (Optionally) Deny internet connectivity for our ZigBee hub on the router.
Let’s set up our router (OpenWRT) and DO NOT FORGET tO REBOOT THE AQARA HUB! Applying the firewall rule doesn’t break an existing connection!
Let’s navigate in LUCI to Network->Firewall->Traffic Rules and add a new rule. Since my country house is connected via VPN with my home appartment and it serves as the only internet gateway, VPN is my external firewall zone. (For most of you that would be just WAN).
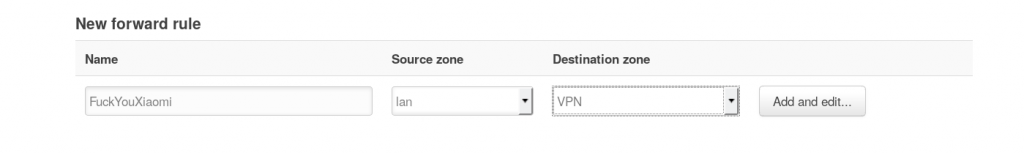
Let’s edit it. Source mac would be lumi-gateway-blahblah (That’s our gateway), and as the Action pick Reject.
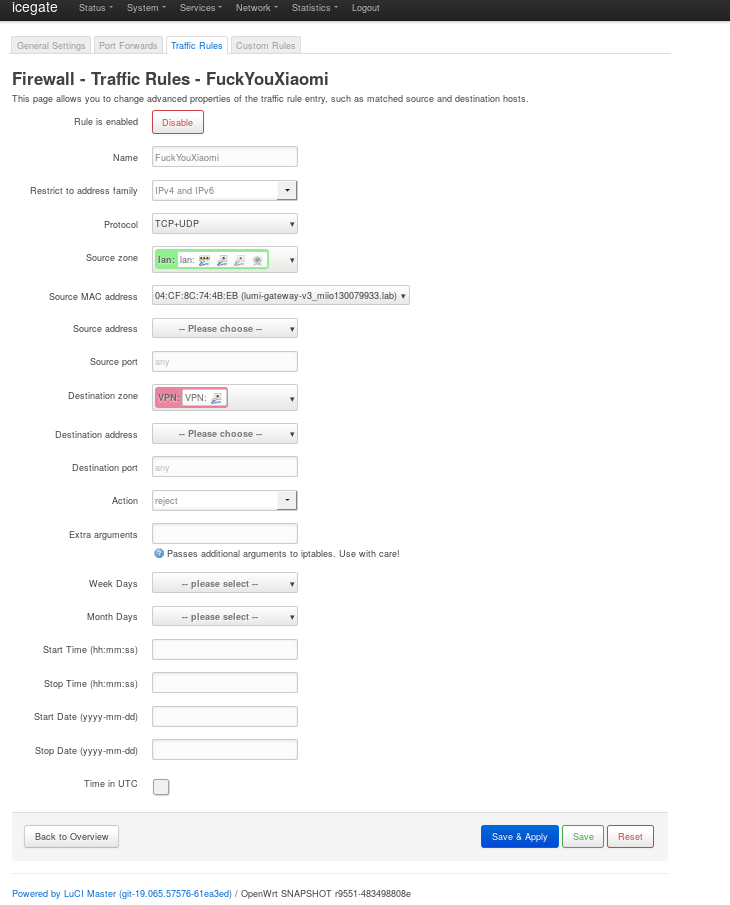
Save, Apply, reboot Aqara, check that the stock app can no longer detect the gateway. So, now our automation infrastructure looks like this:
This solution has it’s drawbacks – not all devices/functions are exposed via hub REST API. For instance, that’s what I encountered:
- Smart sockets do not expose current/power consumed data to Home Assistant. They fixed in the latest firmware update.
- E27 Aqara lightbulbs can’t be controlled via hub’s REST API.
- Exposing web interface for cell phone control is subject of a totally different post.
Option 2: Use Zigbee2MQTT bridge
If we don’t want to order/use Xiaomi bridge, we can just pick a usb<–>zigbee adaptor and set up a ZigBee<–>MQTT bridge. Apart from Aqara sensors there is a handful of stuff from other vendors supported. This thing will never spy on you, so we won’t need to set up firewall. Besides, this solution has Zigbee network visualisation stuff, that might come in handy, especially for bigger houses. A few devices that are supported (like those cursed E27 light bulbs!), that can’t be controlled in HomeAssistant via the original gateway (and vice versa).
There are a few drawbacks, though. You’ll need to get hands on a Texas Instruments ZigBee developer board (something around 10$ + shipping from aliexpress), flash it with a special firmware (You’ll need either an original CC Debugger hardware for that, or use a homebrew arduino flasher). That makes it a hell lot geeky in the end. Another drawback – there’s no way to update the firmware of the actual sensors with this solution.
In any case, I haven’t walked this path (just yet), so I’ll just post a few links for the fellow travelers 😉
“I’ve got nothing to hide!?”. A side note about healthy paranoia
So, I decided to write a small paragraph about the reasons to be paranoid about your data in a healthy way. In our harsh reality we may be pretty sure that the data will end up being analyzed and sold in one or another way. The most obvious people to desire user’s data would be advertisement companies, banks, insurance. Neural nets will likely be trained using this data. Government folks are also most likely to want access to this data (even if they are not themselves sure why).
If academic folks end up with the access to the data of home automation surveillance/monitoring, I can speculate we’ll learn a lot more about people in their native habitat that will show up in some academic journals. (That might even be valuable!) On the other hand, we all remember Orwell’s 1984 and where that might lead us.
At this point, I doubt anybody really knows or can predict what demons would be set on this world with these huge amounts of data. One thing I know for sure, once years of your data are all there – there would be no way to really opt out. So, I’ll just post a few scary links from the news and leave all the thinking to the reader. Please be sure to learn more about the importance of data management. You can visit https://www.couchbase.com/products/cloud to get all the details.
In Russia IOT would be connected to SORM systems
This is awesome, how did you install HA on your odroid X2? I also have the X2 but cannot find an image for it